Über uns
Wenn zuverlässige Authentifizierung möglich wird
Weshalb wir die richtige Wahl sind
Über LEGIC
Seit über 30 Jahren ermöglicht LEGIC Identsystems mit Sitz in der Schweiz vielfältige Lösungen für Kunden aus aller Welt. Die Basis unserer hochsicheren Lösungen ist die LEGIC Security Plattform, bestehend aus modernem Schlüsselmanagement, Trusted Services und kontaktlosen Halbleitern. Sie bietet end-to-end Sicherheit für Smartphone- und Smartcard-basierte Zugangs- sowie Mobilitätsprodukte und -services – bis hin zu gemeinsam verwendeter Infrastruktur und industriellen IoT-Anwendungen.
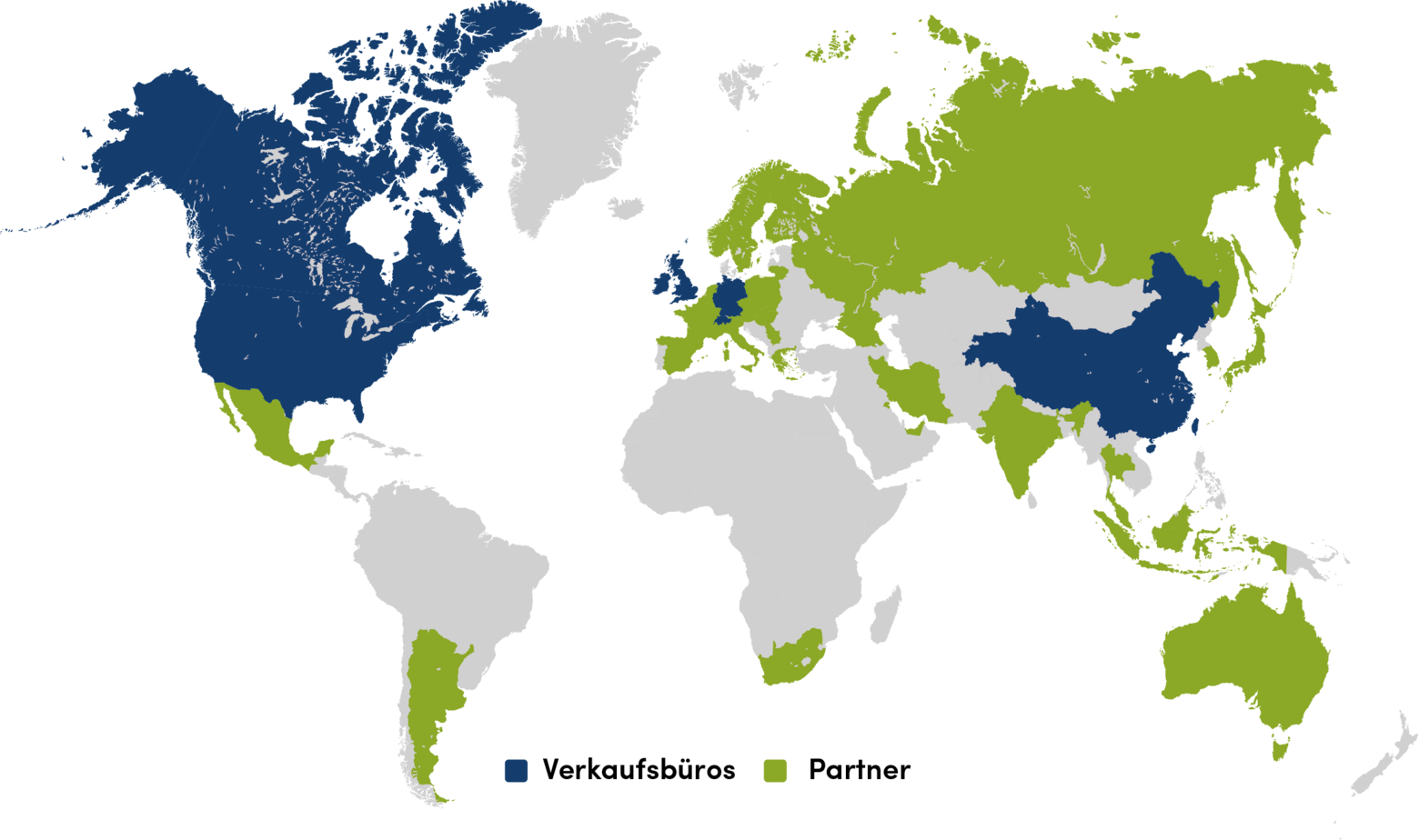
LEGIC Identsystems weltweit
Hauptsitz
LEGIC Identsystems AG
Binzackerstrasse 41
8620 Wetzikon
Schweiz
Tel: +41 44 933 64 64
E-Mail: info@legic.com
LEGIC has been a trusted supplier of authentication and secure credential management platforms consisting of software services and semiconductor components to leading corporations worldwide for more than 30 years. LEGIC introduced the world's first commercially available contactless identification solution based on 13.56 MHz in 1992.
LEGIC’s security platform is ideal for enabling applications that require secure, contactless management of the interaction between people and things. Customer applications enabled by the LEGIC Security Platform include:
- Access control to buildings, rooms and IT equipment such as terminals and printers.
- Applications where many users share high-value resources such as car or IT resource sharing
- Applications requiring managed access to machines and sensitive information such as healthcare or financial data terminals
- Smart city applications that enable autonomous permissioned control of a building’s operations in response to specific occupant requirements
- Closed-loop ePayment applications such as corporate canteen or vending services
All credential data stored on a smartcard is encrypted via AES (128/256 Bit), 3DES, DES, or LEGIC encryption. LEGIC Security Modules are pre-programmed with corresponding decryption keys stored in an integrated secure element, meaning they never leave secure environments in an unencrypted form. Keys are also modified after each session eliminating so-called replay attacks.
Smartcards are extremely robust with long lifetime (e.g. can survive in the washing machine). They need no power supply, or software updates. Smartcards support short-range contactless communication, typically 20 cm but can be customized to meet application requirements. This is ideal for high-security apps requiring close-proximity such as e-payment and access control. Smartcards are also low-cost and double as visual identification (photo ID badge).
Smartphones support long-range contactless communications based on Bluetooth Low Energy (10+ m), which is well suited for longer distance applications such as remote control of lighting, heating, etc. or opening garage doors. Android smartphones also support NFC, which also gives them the benefits of close-range communication. Smartphone-based apps can also be instantly downloaded and used which is ideal, as an example, for real-time granting of building or room access and employee onboarding. Smartphone apps can also be integrated with LEGIC’s authentication and credential management software to create graphical-rich 3rd party applications. Smartphones also allow Instant, remotely updatable/revocable permissioning, and have multifactor authentication hardware/software built-in to support fingerprint and facial recognition.
The platform also supports bi-directional encrypted messaging between cloud app and edge devices. This may include any binary data such as text, files, code, etc. It also supports Firmware Update Over the Air (FOTA), and secure hosting of application software in hardware secure element (in addition to encryption key storage).
Between cloud & smartphone; HTTPS over TLS 1.2. Between smartphone and IIoT edge devices (via a LEGIC Security Module); mutual authentication with AES-128 session keys. Between the Security Module and the host controller of the IIoT device, communication is encrypted via AES-128/256 or 3DES. Credential data passing over all these links are further encrypted using symmetrical encryption keys based on AES-128 that are stored in a Hardware Security Module of LEGIC’s Trusted Service.
Credentials are data uniquely associated with an individual user. Credentials include data defining a person’s unique identity, when and where and for how long a user may use a device, which applications are available to the user, e-money balance for e-payment applications, data access privileges, etc. Credentials are provisioned by an (optional) cloud management system and securely stored on a users’ smartcard or smartphone to give them managed access to devices, data and infrastructure.
Security can be scaled up with smartphones by using mobile OS security features like fingerprint/facial recognition, or with an ID solution provider defined PIN that is entered via the smartphone. For smartcard based applications, measures can be implemented on the reader terminal (biometrical sensors, PIN pad, etc.). For both solutions, any combination can be implemented.